About a month ago, one of the most interesting pieces of news came about Apple and specifically the M1 Mac. This story revolved around the Silver Sparrow malware, a mysterious computer virus that hasn’t given us any new answers, despite being more than a month old at the time of writing.
In this post, I’m going to cover everything Mac owners need to know about this malware, including what we know about it, if you’re at risk, how to tell if you’re infected, and how to prevent similar attacks in the future.
Let’s get into it!
Contents
- What is the Silver Sparrow malware?
- How does Silver Sparrow infect a Mac?
- Is the Silver Sparrow malware dangerous?
- Has Apple fixed the Silver Sparrow malware problem?
- How to tell if you have Silver Sparrow malware on your Mac
- Can your Mac still be infected by Silver Sparrow (April 5th, 2021)?
- Malware vs. Proof of Concept: Understanding Silver Sparrow
- Silver Sparrow isn’t the first time this kind of attack has targeted Apple
- How to protect your Mac against malware in the future
- The Silver Sparrow malware story seems to be over – for now!
What is the Silver Sparrow malware?
The Silver Sparrow story broke on February 22, 2021, though research had already gone into uncovering it as early as January. A cybersecurity firm known as Red Canary (how ironic) was the first to detect it.
According to Red Canary, the Silver Sparrow malware (which comes in two variations) first picked up activity in August of 2020. This first version was designed to infect Macs with an x86 architecture. In December of 2020, a new version began to appear, infecting M1 Macs.
In January and February of 2021, Red Canary detected the first and second versions of the Silver Sparrow attack and started to alert the public of it, hoping to “clip its wings” before it had a chance to do any real damage.
I recommend reading the full Red Canary write-up for more information.

I still don’t get it…
In short, Silver Sparrow is a computer virus that was built to specifically infect the new M1 Macs. This is a big deal since these Macs are being touted as the future of Apple’s computer lineup.
That’s why when the story first broke, it went viral. A vulnerability of this scale (tens of thousands of Macs were reported to be infected, which means many more tens of thousands could still be infected unknowingly) has the potential to completely wreck all of the new M1 purchases and ruin confidence in these new machines.
So that’s the basics of why this is a big deal and why there’s more concern surrounding it than a typical Mac virus. It’s infected a large number of computers that have only been on the market for a few months, is positioned in such a way that it could deliver a devastating payload to infected computers, and spread rapidly.
How does Silver Sparrow infect a Mac?
This is one of the most fascinating parts about all of this:
No one knows how it infected any of the Macs (yet).
The Silver Sparrow Malware seems to have appeared out of nowhere. And while the engineers at Red Canary have some theories, the truth is that for now, we have no clue where this virus came from or how it ended up on users’ computers.
The general theory (at the time of writing) is that it most likely came from malicious search engine results (per Red Canary). This means that users were probably using a search engine like Google, clicked on a malicious link in the results, shortly after which the Silver Sparrow package was installed on their Mac.
It’s unknown, however, what initiated the download for any of the infected Macs. In my opinion (as a writer, not a security expert), this is the most concerning aspect of the attack. Because if you don’t know how it was installed or where it came from, then it becomes very hard for users and Apple to prevent this from happening again.
Is the Silver Sparrow malware dangerous?
No – but you should still be concerned. After a lot of analysis, it appears that there isn’t anything malicious going on in the Silver Sparrow malware. This has caused some to question if it can really be called “malware” if there is no malice, but I’ll go into that more later.
On the other hand, it would be naive to assume that just because this is a benign malware attack that there is no cause for concern. It’s still a large virus with a fast infection rate and a high degree of success. Silver Sparrow could’ve easily wreaked havoc – we just got lucky that it didn’t.
The closest thing that has been found to an “intention” in the Silver Sparrow software are messages left throughout it. In the first version of Silver Sparrow, which targeted x86 Macs, a binary file was found that contains the message “Hello, World!”. In the second M1 version, another binary was found with the message “You did it!”.
While “Hello, World!” is a commonly used phrase in programming, it’s hard to ignore the unsettling undertone. After all, this is a malware attack that caught global attention. And the ominous words “You did it!” are far from comforting.
Some have speculated that Silver Sparrow was a failed attempt at infecting Macs. The idea is that the missing payload (i.e., the threat to users) is evidence that whoever sent it out must have forgotten to include the payload. Though a bit fun to consider, the efficiency and effectiveness of the malware make this seem unlikely.
Has Apple fixed the Silver Sparrow malware problem?
Apple has fixed the Silver Sparrow malware issue. If you don’t already have this on your Mac, you aren’t going to be infected by it. Almost immediately, Apple revoked the certificates of developer accounts that had signed the Silver Sparrow packages, preventing any more from being installed on macOS machines.
In plainer terms, Apple has very strict rules over what can and can’t be installed on your Mac. It’s a common complaint thrown against Apple, that developers have to have special licenses and use specific tools to develop apps for macOS.
Because of these rules, the Silver Sparrow software had to be “signed” by a certified Apple developer account. Apple identified the accounts that were used to achieve this attack and revoked their validity, stopping this instance of Silver Sparrow in its tracks.
I’m sure Apple has also been working behind the scenes over the last month to rework macOS and the next M1 chip (M2?) to prevent this from happening again. That said, you should know that Apple has only stopped this current wave of Silver Sparrow attacks. Because of the lack of information surrounding this attack, similar strategies could still be used in the future.
How to tell if you have Silver Sparrow malware on your Mac
Since Silver Sparrow doesn’t appear to do anything malicious at this time, it can be tough to know if your Mac is infected without going out of your way to check. Additionally, the main way to uncover Silver Sparrow on your Mac isn’t guaranteed to work, though it does work for the vast majority of users.
Finding the ._insu file
The first method for finding is to look for a file in your Library folder titled ._insu. This is usually the only file most users find, as it’s the file that tells the Silver Sparrow malware to delete itself from your Mac.
By default, the Library folder is hidden from you. That’s because it has tons of sensitive files and folders in it, and Apple doesn’t want users accidentally breaking their Macs. So be warned – don’t delete, move, or otherwise alter anything in this folder! You’re just looking to see if ._insu is there.
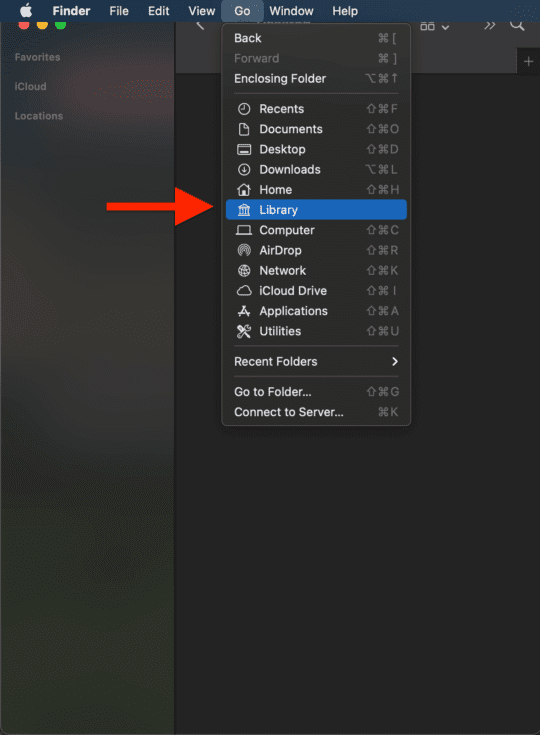
To do this, open Finder. In the Menu Bar, you should see a dropdown menu labeled Go. Click this menu, then hold the option key. This will cause the hidden Library folder to appear.
Clicking on this will bring you into your Library folder. Once there, scroll through and check for files labeled ._insu. You shouldn’t need to look through any of the folders present in your Library folder. If you don’t see it here, then you should be safe.
Using a third-party malware detector
As mentioned, the above method won’t work for everyone. If you don’t see the ._insu file, then I’d say you’re probably safe. But if you want to be really sure, and you aren’t experienced in this sort of thing, then I’d recommend using a third-party solution.
Specifically, Malwarebytes is a good option. In addition to being a generally recommended piece of software, Red Canary worked directly with Malwarebytes to get an idea of how many Mac users were infected with Silver Sparrow. So Malwarebytes is specifically configured to detect the Silver Sparrow malware.
You can install Malwarebytes on your Mac for free for two weeks, which should be plenty of time to determine if you have Silver Sparrow on your Mac. After that, you can keep it on your Mac for just $3.33/month. I am not sponsored by Malwarebytes, it’s just a solid app.
Can your Mac still be infected by Silver Sparrow (April 5th, 2021)?
To the best of everyone’s knowledge, no! You cannot still get the Silver Sparrow malware on your Mac. If you don’t already have it, you should be good to go. The day after the news of Silver Sparrow broke, Apple revoked the certificates of the developer accounts that signed the Silver Sparrow software.
This means Silver Sparrow shouldn’t be able to install on your Mac in the background. Apple doesn’t let unsigned software install on Macs without admin permission. So don’t install anything unsigned (which you should never do anyway) and you’ll be safe from the current version of Silver Sparrow.
Malware vs. Proof of Concept: Understanding Silver Sparrow
As we approach the end of this article, I want to take a moment to expand on some of the ideas, mysteries, and concerns surrounding the Silver Sparrow malware, because by all accounts it’s a very interesting incident.

First, I want to cover the difference between malware and a proof of concept. The first, “malware”, is a term that most people have been applying to Silver Sparrow. Malware refers to malicious software (hence the name). So if there isn’t any clear malice involved, is Silver Sparrow truly malware?
And that brings me to the second point, which is that a significant number of people are theorizing that Silver Sparrow might just be a proof of concept. A proof of concept is an application that proves that something can be done – and that’s it.
For instance, if you wrote an app that calculates a user’s age based on their typing style, but didn’t sell it or implement it into any other application, then that would be a proof of concept. You would prove that this theory is now possible and executable.
At first glance, Silver Sparrow does seem like it could be a proof of concept gone wrong, sent out and spread when it wasn’t meant to. In other words, this “attack” was just a programmer experimenting.
Now, this doesn’t mean that Silver Sparrow isn’t also malware. One of the basic definitions of malware is a piece of software that gains unauthorized access to a person’s computer. Silver Sparrow does this.
However, many experts think the proof of concept theory is unlikely in this instance, given how widespread Silver Sparrow is. They believe it’s more likely that Silver Sparrow still has some underlying motive that we aren’t yet aware of or that it was meant to be a threat but failed.
Silver Sparrow isn’t the first time this kind of attack has targeted Apple
It’s important to note that this isn’t the first time a malware attack of this scale has targeted Apple. The Silver Sparrow malware is certainly one of the more mysterious instances, but Apple has faced challenges like this before.
In fact, an M1-specific malware was discovered just four days before the team at Red Canary published their findings on Silver Sparrow. This prior malware, labeled “GoSearch22“, is more run of the mill. It puts ads all over your Mac to malicious websites and collects sensitive data in the background.
Also, Silver Sparrow is at least the sixth major notarization failure from Apple. This means that six times prior, Apple’s automated notarization process has failed to detect malware and allowed it to install on users’ devices.
And now that Apple has made it easy for developers to create apps that run on x86 and M1 Macs, you can expect many malware and virus developers to use these tools to create M1-compatible versions of their malware.
In short, malware and viruses are nothing new. Silver Sparrow is just a reminder to take these concerns seriously and protect yourself against attacks as best you can.
How to protect your Mac against malware in the future
And that brings us to the end of this article: Protecting yourself against attacks like the Silver Sparrow malware in the future. There are a few ways you can do this, though it should be noted that if someone really wants to disrupt your Mac, they’ll find a way to do it. Like stopping a lockpicker, you can’t stop the attempt completely, you can only do your best to dissuade an attack on your device.
In researching how to protect Macs against malware attacks, I kept running into the same piece of advice: Don’t install antivirus!
At first, I thought this must just be a handful of overconfident users. But after more extensive research, it seems that a sizable portion of security advisors for Mac believe that antivirus does more harm than good. It nags users, costs money, becomes outdated easily, and takes up a lot of processor power, slowing down your Mac.
Instead, the advice I found was to install a malware detection application (like Malwarebytes). These apps don’t prevent anything from happening, per se, but instead keep your Mac clean, help you avoid risky websites, and let you know if anything on your Mac looks fishy.
This, coupled with safe habits, should be plenty for most users. Don’t install anything on your computer that you aren’t sure is safe, don’t pirate or torrent, stick to trusted websites, don’t click on ads or big green Download buttons, and avoid pornographic web outlets. If you do all of these things and use a malware detection application, you should be alright.
The Silver Sparrow malware story seems to be over – for now!
I hate to end things on an ominous note, but the truth is that even the experts have a limited understanding of what this software did, where it came from, why it was created, and if a similar attack is being planned in the background.
For these reasons, I recommend everyone keep an eye out, be wary about their internet usage, and stay up to date with the AppleToolBox blog so you can stay informed about all things Mac.
Until next time!










Write a Comment