SSH is a network protocol that can help you use a secure way to access a computer over an unsecured network. It’s mostly used for remote logins. It stands for Secure Shell or Secure Socket Shell. Below we’ll cover more in-depth what it is and how to use it.
What is SSH?
As mentioned above, SSH is a security protocol, specifically an encrypted connection protocol. It may also refer to the utilities that run the SSH protocol. It can provide strong password authentication, encrypted data communications and public key authentication.
SSH helps you securely connect to a remote server using hashing, symmetric encryption and asymmetric encryption.
By default, it runs off the Transmission Control Protocol (TCP) port 22, however, that can be adjusted.
Using SSH to Access your Mac from Another Computer
Start by setting up Remote Login:
- Click the Apple icon.
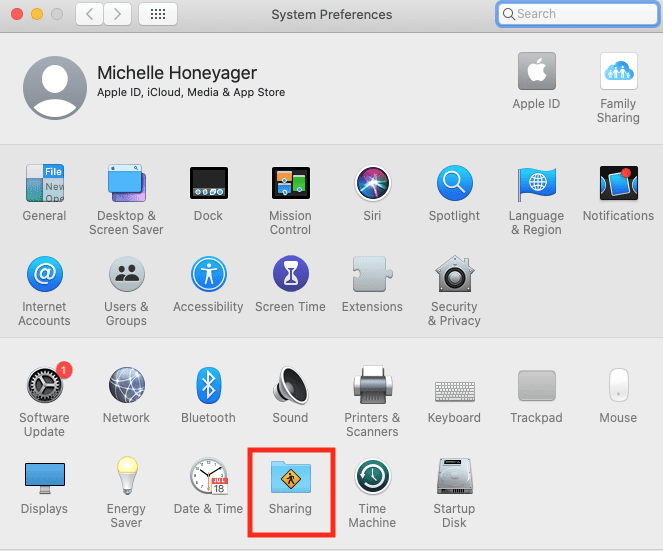
- Select System Preferences.
- Click on Sharing.
- Then select Remote Login and click on the Remote Login checkbox so that it’s checked.
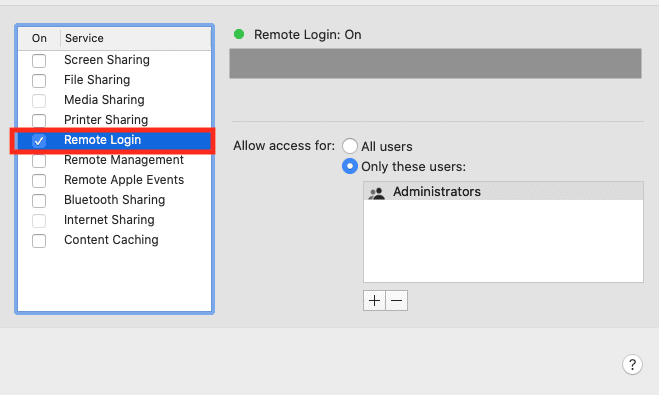
- You can either specify all users or only certain users using the Add (+) button.
If you’re using Ventura, you may need to access this area by going to the Apple menu > System Settings > General > Sharing. You may also click the i Info button and check Allow full disk access for remote users.
To log in to your Mac from a different computer:
- Using the other computer, open the Terminal (Go in Finder > Applications > Utilities > Terminal). You might also use a different SSH client.
- Type in the following SSH command and then hit enter (return): ssh username@IPAddress (adding your own username and IP address)
- You’ll be prompted to enter your password. Do so and then hit enter.
To find your user name and IP address, click on Remote Login on the Sharing screen and hit the checkbox to turn it on. It will show the command you need to enter, which might show a .lan name in place of the IP address.
SSH Certificates
SSH also uses public and private keys instead of passwords to connect. As the name suggests, the public key can be shared. Private keys stay with the computer, never get typed and so stand less of a chance of getting stolen than passwords. Some connections use key pairs, which require using a private and public pair. You may have to upload the public key.
You generate the keypair by entering a specific command into Terminal. The general command is ssh-keygen -t rsa, though some networks will have more specified commands for anyone who wants to access their system to follow.
Certificates go above and beyond using public keys. The way certificates tend to work is you would have to transfer public keys, get them signed by a CAs (or Certificate Authority) and then have the keys returned. Certificate Authorities are organizations or trusted third parties that validate identities, and then they bind those identities to keypairs that have digital certificates.
You can also import trusted certificates into the System Keychain using the following command lines in Terminal:
- On newer systems like Monterey and Ventura: sudo security add-trusted-cert -d -r trustAsRoot -k /Library/Keychains/System.keychain <certificate>
- On older Mac systems: sudo security add-trusted-cert -d -r trustRoot -k /Library/Keychains/System.keychain <certificate>









Write a Comment